- The tip of a swordfish bill that was found embedded in a deep-sea mooring. The memento has come to represent the challenges WHOI engineers and researchers face each time they deploy a mooring. “It reminds me that when we put things in the ocean, the unthinkable can sometimes happen,” said Rick Trask, manager of WHOI’s Mooring and Rigging Shop.
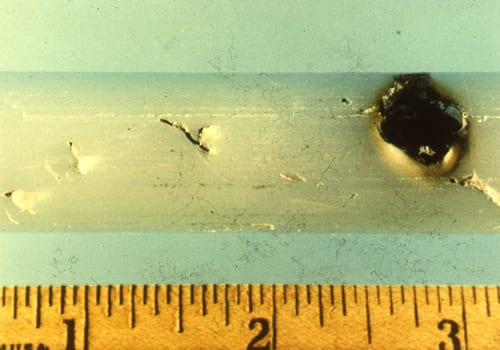
- Mooring lines made of wire rope covered with plastic also sustained damage that looked like fish attacks. On this segment of line, the plastic jacket suffered a puncture (round hole at right) and several cuts (diagonal marks left of the hole). Suspecting that bumps in the line near the cuts might be bits of teeth, WHOI engineers x-rayed the line (see next photo).
- Mooring lines made of wire rope covered with plastic also sustained damage that looked like fish attacks. On this segment of line, the plastic jacket suffered a puncture (round hole at right) and several cuts (diagonal marks left of the hole). Suspecting that bumps in the line near the cuts might be bits of teeth, WHOI engineers x-rayed the line (see next photo).
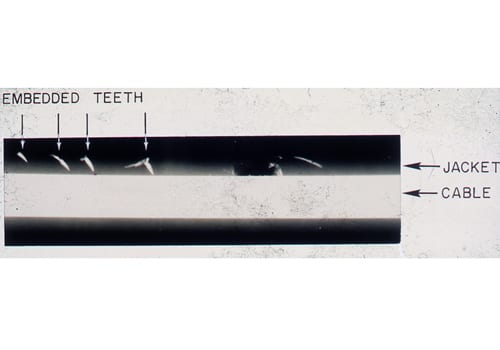
- An X-ray of the jacketed wire rope seen in the previous photo shows fragments of fish teeth embedded in the plastic jacket—hard proof that fish bite mooring lines.
- The tip of a fish tooth that broke off inside a mooring line. The tooth, from the lower jaw of the deep-sea species Sudis hyalina, has fine serrations that enable it to cut cleanly through ropes made of synthetic fibers. Sudis grows to more than a meter in length.
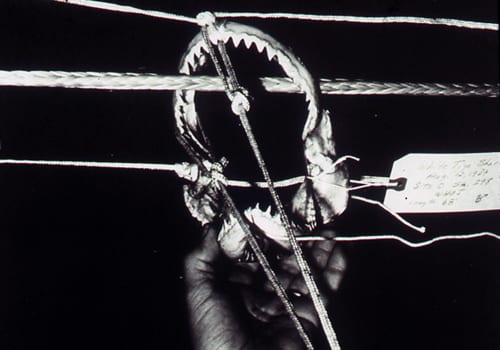
- A skull of the deep-sea fish Alepisaurus ferox, whose long, sharp teeth can inflict major damage on mooring lines and instruments.
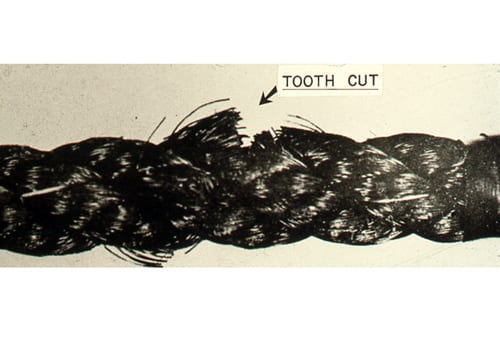
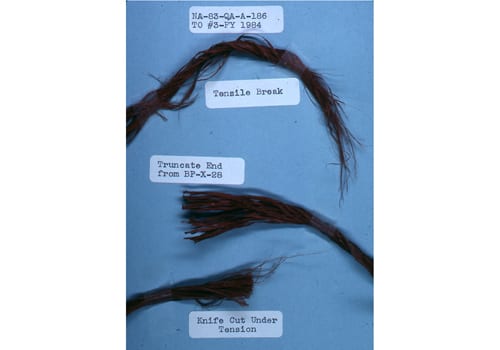
- Occasionally, a synthetic mooring line was recovered with two very different kinds of damage: Some fibers had clean, blunt ends while others had frayed, ponytail-like ends. WHOI engineers concluded that the clean cuts were inflicted by biting fish and the frayed ends resulted when the remaining intact fibers were unable to bear the full weight of the mooring, and pulled apart under tension.
- WHOI engineers compared mooring lines they thought had been cut by fish (center) with ropes damaged in the rigging shop by knife blade (bottom) or by being pulled apart under tension (top).
- Buoy Group engineers subjected wire rope, four kinds of synthetic rope, and several kinds of sheathing materials to 14 kinds of damage in hopes of identifying how rigging breaks, and what kinds of rigging hold up best against fish attack. Here, an engineer simulates how a shark could cut a synthetic rope pulled taut by the weight of attached instruments.
- WHOI engineers developed the “Bitemeter” to measure the force needed to drive a sharp object, such as a shark’s tooth, into rigging components and to test the ability of those components to resist punctures by fish teeth. “It took a long time before we developed moorings that were resistant to sharks,” recalled former WHOI scientist Ferris Webster.
- The introduction of jacketed wire rope in the mid-1960s solved some major problems for the Buoy Group—it was harder to cut and could withstand the elements better than synthetic rope. But wire rope was still vulnerable to attack: If a fish tooth punctured its plastic jacket, corrosive sea water would cause the wire rope within to rust, putting the mooring at risk.
- Fish attack instruments as well as rigging. This Vector Averaging Current Meter was attacked by a fish large enough to get its jaws around the 8-inch diameter casing.
- Running a mooring line through human hands as it’s being reeled back aboard ship helps locate cuts, holes, and gouges caused by fish.
- Engineer Henri Berteaux of WHOI and MIT co-wrote the Fishbite Handbook (with Bryce Prindle) as well as leading texts on buoy and mooring design.
Image and Visual Licensing
WHOI copyright digital assets (stills and video) contained on this website can be licensed for non-commercial use upon request and approval. Please contact WHOI Digital Assets at images@whoi.edu or (508) 289-2647.